Blogs
Minerva to Stop the Run of GhostMiner that is Solely Trying to Mine Monero

In 2018, the cybercriminals are depending on malicious cryptocurrency miners who are using advanced exploit kits to make money online. The case of WaterMiner in late 2017 became quite popular. The security aspect was stepped up by the companies by upgrading their detection capabilities. However, the cybercriminals, as observed in the past, always remain a step ahead of the security vendors.
Recently, the research team of Minerva had detected a new malware called GhostMiner that is ‘killing’ existing miners to become the sole miner of Monero (XMR). This way GhostMiner was earning more XMR and depriving other miners. The research team of Minerva dissected GhostMiner after it had stopped the entry of the mining malware at a customer site. Such malware, as described by the Minerva team are using advanced fileless techniques to mine cryptocurrencies. It is, therefore, becoming increasingly difficult to identify the mining malware. However, Minerva Labs have succeeded in saving the Monero miners by the turning the tables on GhostMiner and using their scripts to remove them.
How GhostMiner Affected Monero
- Using Advanced Fileless Techniques
The core activity of the mining malware, GhostMiner was executed by a compiled malicious Windows executable. PowerShell evasion frameworks like Invoke-ReflectivePEInjection and Out-CompressedDll gave the leeway to the executable to hide from the detecting agents. They used fileless techniques to mask the presence of GhostMiner. ps1, a PowerShell script had the role infecting new victims while another script of PowerShell (WM164.ps1 on x64 machines) was charged with mining Monero (XMR).
The path taken by GhostMiner successfully bypassed many security detectors and some of the analyzed payloads even remained fully undetected. However, the malware was detected by the same security vendors after the fileless technique was removed. Memory Injection Prevention of Minerva prevented the malware from making a fileless attack. Thus, the malware did not spread out and can no longer mine Monero (XMR) or any other cryptocurrency.
- GhostMiner Targeting New Victims
Neutrino.ps1 searched out and attacked servers that run MSSQL, phpMyAdmin, and Oracle’s WebLogic. The attack mainly focused on the WebLogic servers and thus randomly searched out IP addresses, created multiple TCP connections. The core component of this attack conversed with its C2 server over HTTP. The process included encoding requests and answers in Base64. The indicators used by Minerva to detect the malware attacking Monero miners show that GhostMiner had created the malevolent HTTP requests to hide in companies with Chinese speaking users. Not all the techniques used by GhostMinerare new but it is the first time that a malware has used all of them together. The research done by Minerva shows that the operators of GhostMiner put a lot of effort into assembling their code. The attack launched on the Monero miners clearly rings the bell of warning for the security vendors.
Minerva’s Fight Against the Malevolent Crypto-Jacking Software
GhostMiner started its Monero mining operations only after it had eliminated all possible competition that they detected. The research team of Minerva capably analyzed the techniques that were deployed by the malicious malware. The script that turned the tables on the mining malware was named as MinerKiller.
- PowerShell’s “Stop-Process-force” command was used to identify the running Monero miners and then eliminate them. They used a hard-coded blacklist to detect the miners.
- The extension exe was used to stop and remove miner blacklisted services.
- The researched team eradicated miners that run by the task name using exe as blacklisted scheduled tasks.
- Commandline arguments were interpreted, analyzed and then used to stop and eliminate the miners.
- Another strategy employed by Minerva was to go through the list of established TCP connections and identify the ports linked with the miners. The data were collected using
Conclusion
According to the Minerva team, one way of fighting mining malware like GhostMiner for the security vendors is by writing their own PowerShell scripts. It will help in identifying the unfamiliar tasks, services, and processes by arguments and TCP connections. These features will hopefully ward off any attempts of the cybercriminals in the mining process of cryptocurrencies.
We will be updating our subscribers as soon as we know more. For the latest on XMR, sign up below!
Disclaimer: This article should not be taken as, and is not intended to provide, investment advice. Global Coin Report and/or its affiliates, employees, writers, and subcontractors are cryptocurrency investors and from time to time may or may not have holdings in some of the coins or tokens they cover. Please conduct your own thorough research before investing in any cryptocurrency and read our full disclaimer.
Image courtesy of Bart via Flickr
Altcoins
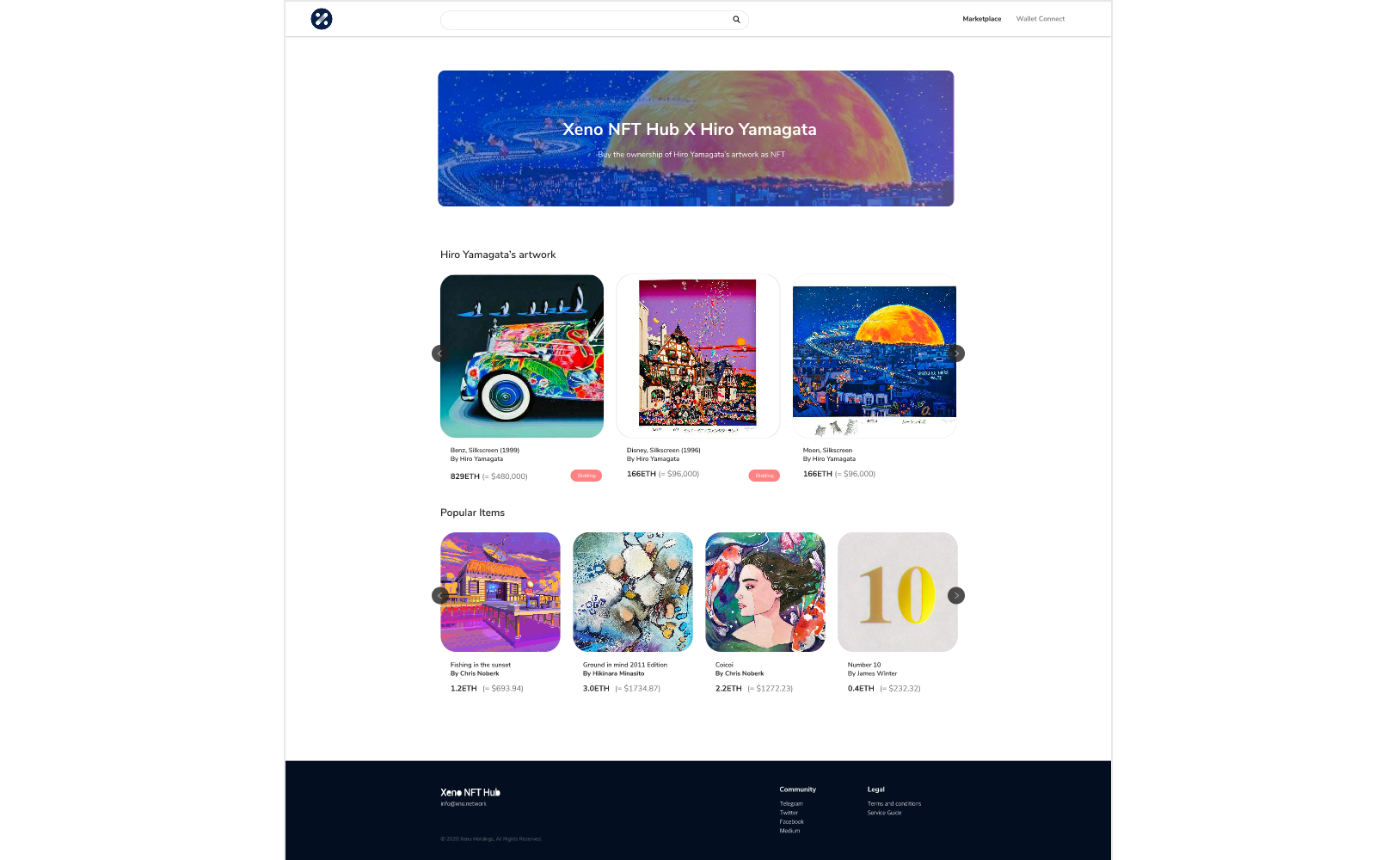
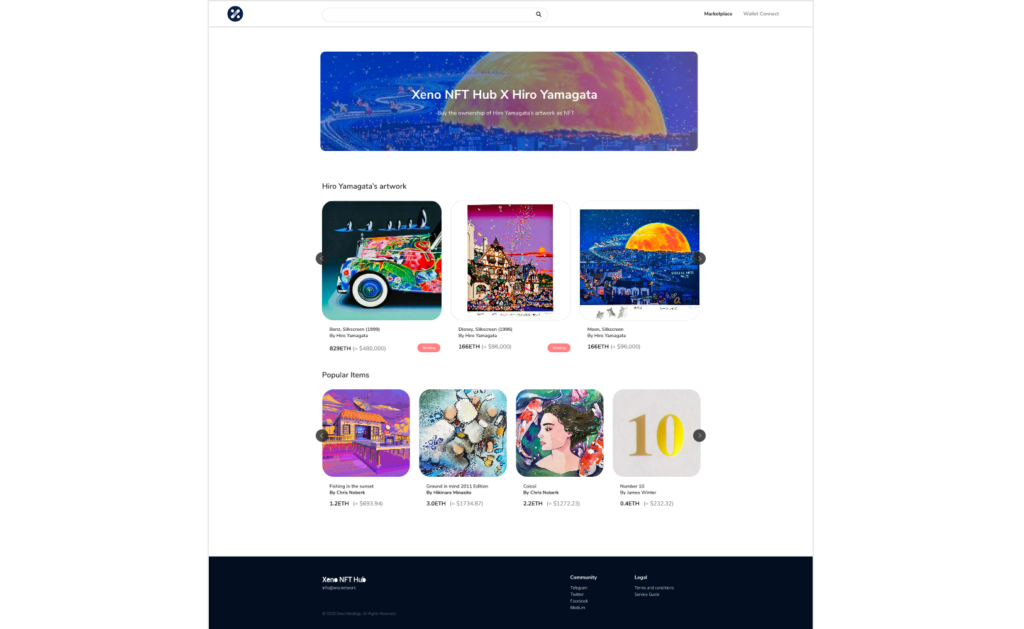
XNO Token of Xeno NFT Hub listed on Bithumb Korea Exchange


Hong Kong, Hong Kong, 25th January, 2021, // ChainWire //
Xeno Holdings Limited (xno.live ), a blockchain solutions company based in Hong Kong, has announced the listing of its ecosystem utility token XNO on the ‘Bithumb Korea’ cryptocurrency exchange on January 21st 2021.
Xeno NFT Hub (market.xno.live ), developed by Xeno Holdings, enables easy minting of digital items into NFTs while also providing a marketplace where anyone can securely trade NFTs.
The Xeno NFT Hub project team includes former members of the technology project Yosemite X based in San Francisco and professionals such as Gabby Dizon who is a games industry expert and NFT space influencer based in Southeast Asia.
NFT(Non-Fungible Token) technology has recently gained huge focus in the blockchain arena and beyond, making waves in the online gaming sector, the art world, and the digital copyrights industry in recent years. The strongest feature of NFTs is that “NFTs are unique digital assets that cannot be replaced or forged”. Unlike fungible tokens such as Bitcoin or Ether, NFTs are not interchangeable for other tokens of the same type but instead each NFT has a unique value and specific information that cannot be replaced. This fact makes NFTs the perfect solution to record and prove ownership of digital and real-world items like works of art, game items, limited-edition collectibles, and more. One of the ways to have a successful…
Altcoins
Should Crypto Projects Devote Resources to Community Growth and Marketing?

2020 has been an incredible year for crypto as investors have generated windfall profits and crypto projects have seen their businesses gain the spotlight they’ve been looking for. While Bitcoin has received most of the attention after major institutional investors announced they were accumulating the increasingly scarce asset, many altcoins have also seen their fair share of glory. When looking at all the big winners of the past year, the first project that probably comes to mind is Chainlink, having appreciated by more than 550% YTD and now valued at over $4.5 billion. But, the actual biggest winner of the year is HEX with a YTD return of over 5,000%.
I mention both of the above projects as they have each taken slightly different paths to achieve greatness. Chainlink has devoted resources toward building a fundamentally sound business with many strategic partnerships while HEX has spent vast sums of money on marketing and promotion. Both approaches are valid, but one thing is certain, it is absolutely imperative for crypto projects to let the crypto community know what makes them special. Of course, one of the reasons that makes crypto so valuable is the powerful blockchain technology that most projects are utilizing.
Cryptocurrency vs. Blockchain Technology
It’s important to make a distinction between blockchain technology and cryptocurrency. Although they are often used interchangeably, they are different. Blockchain technology and crypto were both created after the 2008 financial crisis, but cryptocurrency…
Altcoins
XENO starts VIP NFT trading service and collaborates with contemporary artist Hiro Yamagata
Hong Kong, Hong Kong, 24th December, 2020, // ChainWire //
The XENO NFT Hub (https://xno.live) will provide a crypto-powered digital items and collectables trading platform allowing users to create, buy, and sell NFTs. Additionally it will support auction based listings, governance and voting mechanisms, trade history tracking, user rating and other advanced features.
As a first step towards its fully comprehensive service, XENO NFT Hub launched a recent VIP service to select users and early adopters in December 2020 with plans for a full Public Beta to open in June 2021.
“NFTs are extremely flexible in their usage, from digital event tickets to artwork, and while NFTs have a very wide spectrum of uses and categories XENO will initially focus its partnership efforts and its own item curation on three primary areas: gaming, sports & entertainment, and collectibles.”, said XENO NFT Hub president Anthony Di Franco.
He also added “This does not mean we will prohibit other types of NFTs from our ecosystem However, it simply means that XENO’s efforts as a company will be targeted into these verticals initially as a cohesive business approach.”
Development and Procurement Lead, Gabby Dizon explained, “Despite our initial focus, we found ourselves with a unique opportunity to host some of the works of Mr. Hiro Yamagata. We are collaborating with Japanese artist Hiro Yamagata to enshrine some of his artwork into NFTs.”
Mr. Yamagata has…
-

 Blogs6 years ago
Blogs6 years agoBitcoin Cash (BCH) and Ripple (XRP) Headed to Expansion with Revolut
-

 Blogs6 years ago
Blogs6 years agoAnother Bank Joins Ripple! The first ever bank in Oman to be a part of RippleNet
-

 Blogs6 years ago
Blogs6 years agoStandard Chartered Plans on Extending the Use of Ripple (XRP) Network
-

 Blogs6 years ago
Blogs6 years agoElectroneum (ETN) New Mining App Set For Mass Adoption
-

 Don't Miss6 years ago
Don't Miss6 years agoRipple’s five new partnerships are mouthwatering
-

 Blogs6 years ago
Blogs6 years agoCryptocurrency is paving new avenues for content creators to explore
-

 Blogs6 years ago
Blogs6 years agoEthereum Classic (ETC) Is Aiming To Align With Ethereum (ETH)
-

 Blogs6 years ago
Blogs6 years agoLitecoin (LTC) Becomes Compatible with Blocknet while Getting Listed on Gemini Exchange















