Tech
Protecting Your Privacy From Mass Surveillance: A Look At The Blockchain Cellular Networks Ensuring Security

Gone are the days of cannons and gunpowder in warfare; guns, bombs, and cold wars have been replaced with cyberwars and an inherent need to reinforce cybersecurity and mass surveillance. This has caused concerns over privacy and has resulted in many players in the mobile devices and networks field to explore ways to strengthen the privacy and security of their products for consumers.
The extent to which mass surveillance violates your privacy varies between those who take action and those who bury their heads in the sand. Let’s take a look at what can be done and where you can find the solution to your privacy concerns.
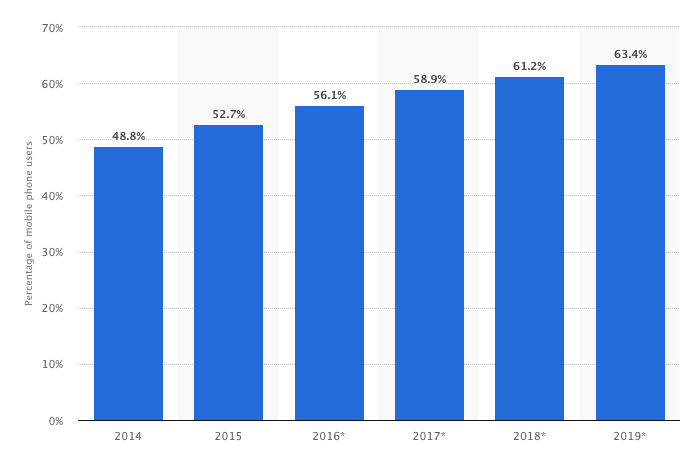
(Graph showing mobile phone internet penetration worldwide from 2014-2019. In 2020, the number of smartphone users worldwide is projected to reach 2.87 billion. Image Source: Statista)
Demand for mobile communication technology continues to grow rapidly around the world. (find stat or graph) The number of wireless subscriptions worldwide was already at 7.7 billion and GSM, LTE and HSPA technologies accounted for nearly all of them. In fact, in the fourth quarter of 2018, the number of LTE subscriptions was around 4 billion.
Coinciding in time is the growth of mobile communication worldwide, increasing mass surveillance, and inherent privacy concerns over the security and privacy of personal and cellular data. Ambitious companies have relentlessly worked towards creating cellular networks that combat security threats. This is no surprise, given the revenue of the security technology and services market was $114.2 billion in 2108.
SIM isn’t just for network authentication, it’s a platform for multiple apps, payments, transit, and other identity-centric features. Your SIM card identifies your device when connecting to your cell network. It also reveals your identity to various services- leaving you with no control over where your data ends up and how it’s used.
How can a cellular network ensure our privacy?
It’s widely understood that the first step towards reducing third party access to your information and minimizing the dangers of your data ending up in the hands of digital giants, is to get a Virtual Private Network. Through which your messages and transactions flow between your device and the connected server within a tunnel-like infrastructure. The encryption on both ends means that your personal and digital data cannot be hacked into.
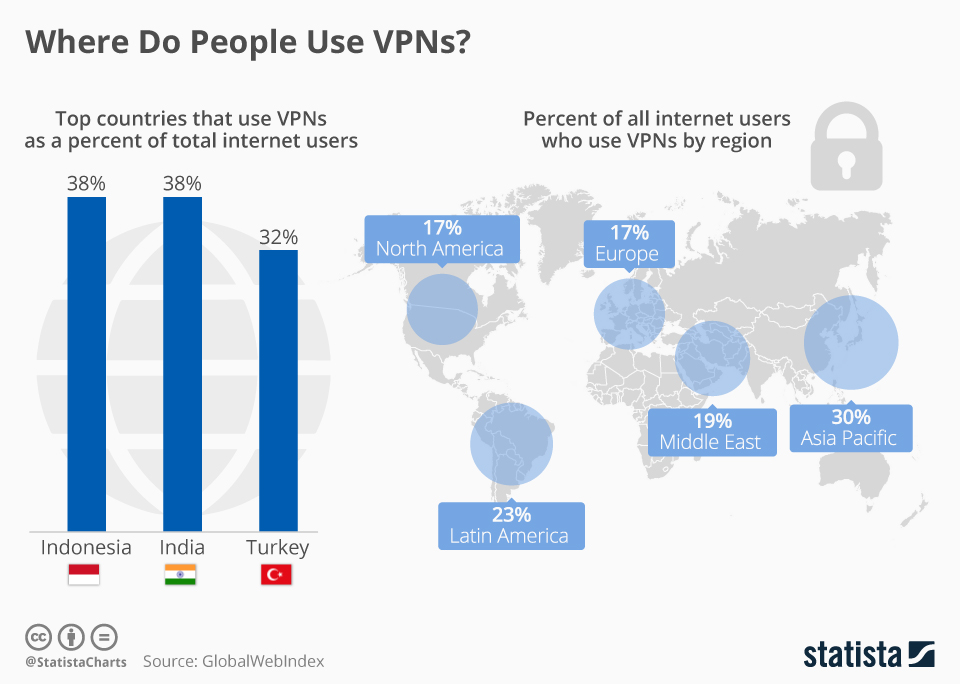
(Image showing VPN usage around the world. Image Source: Statista)
Traditional VPN servers are hosted by a handful of centralised organisations through which each digital transaction, message, phone call, or communication passes through. They’re mostly controlled by commercial entities that store, keep, and sell your personal and digital data.
A quarter of internet users have used a VPN in the past month, with mobile internet access rapidly growing.
So, why then, is there a cause for concern if such VPNs exist and are in high demand? Traditional VPNs essentially store user data on centralised operator servers. Meaning all personal and digital data is readily available and accessible to this central company who can legally sell it.
Anonymous VPNs built to operate on the blockchain do not rely on a central point of control. In a decentralised cellular network with no single authority, the system is automatically made fairer and more secure.
Ano-Phone has too developed an all-inclusive SIM which allows you to stay anonymous online in both, Wi-Fi and Mobile Data networks with its built-in Private VPN for the location of your choice.
Manage your mobile and online identity with end to end encryption to transmit sensitive data to your communication partner peer-to-peer without fears of a man in the middle attack. Your communication is protected from hackers, telecommunications and cloud providers, and mass surveillance, allowing you to operate online privately and securely.
Securely manage your cryptocurrency wallet for Bitcoin on your device. Keeping your privacy in crypto payment systems whilst protecting your online identity and IP addresses. Even blockchain servers cant track your origin IP or personal location details. Ano-Phone encrypts your blockchain transactions and routers them via secure anonymised channels. Meaning they’re safe from man-in-the-middle manipulation attacks.
Switching to a cellular mobile network that understands, values, and provides solutions for your privacy is a sure way to remove yourself from the reach of mass surveillance.
Currency Market
Building Your Nest Egg Brick By Brick: Are Micro-Investments Here to Stay?

No matter what our goals are, sometimes just getting started can be the most difficult part of building our savings up. When it comes to investing, many of us are wary of parting with our money to generate more financial security in the future. But what if you can build significant savings without even noticing?
That’s the aim of the micro-investing apps that have come to dominate online stores across Android and iOS. Today, more fintech startups are working on delivering refined solutions that encourage minuscule investments at a more frequent rate.
Micro-Investing apps will look to make saving more accessible to young people – many of whom in the UK have little-to-no money tucked away for a rainy day.
However, the prevalence of money-saving technology and the disruptive chaos of the COVID-19 pandemic appears to have prompted a widespread increase in households saving more of their disposable income:
With micro-investing platforms playing a role in bringing UK household savings back up to five-year highs, is it fair to say that little-by-little investing is here to stay? Let’s take a look at how micro-investment platforms could revolutionise how we manage our finances:
What is Micro-Investing
Micro-investing, or sparse change investing, is a relatively new development in fintech. It effectively enables users to put away small amounts of money towards their long, or short, term goals. The idea…
Altcoins
XNO Token of Xeno NFT Hub listed on Bithumb Korea Exchange


Hong Kong, Hong Kong, 25th January, 2021, // ChainWire //
Xeno Holdings Limited (xno.live ), a blockchain solutions company based in Hong Kong, has announced the listing of its ecosystem utility token XNO on the ‘Bithumb Korea’ cryptocurrency exchange on January 21st 2021.
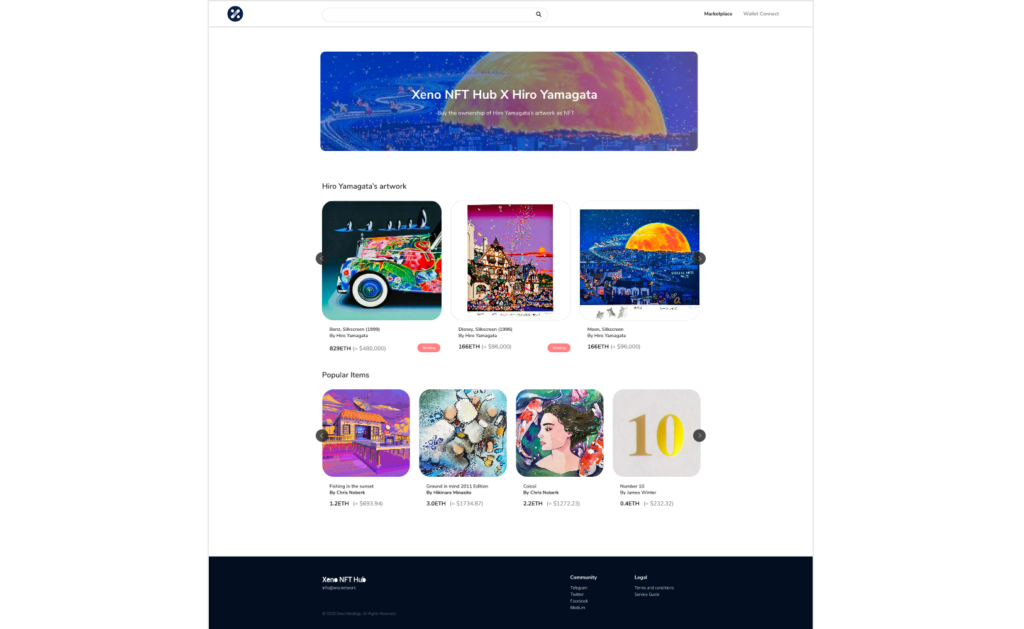
Xeno NFT Hub (market.xno.live ), developed by Xeno Holdings, enables easy minting of digital items into NFTs while also providing a marketplace where anyone can securely trade NFTs.
The Xeno NFT Hub project team includes former members of the technology project Yosemite X based in San Francisco and professionals such as Gabby Dizon who is a games industry expert and NFT space influencer based in Southeast Asia.
NFT(Non-Fungible Token) technology has recently gained huge focus in the blockchain arena and beyond, making waves in the online gaming sector, the art world, and the digital copyrights industry in recent years. The strongest feature of NFTs is that “NFTs are unique digital assets that cannot be replaced or forged”. Unlike fungible tokens such as Bitcoin or Ether, NFTs are not interchangeable for other tokens of the same type but instead each NFT has a unique value and specific information that cannot be replaced. This fact makes NFTs the perfect solution to record and prove ownership of digital and real-world items like works of art, game items, limited-edition collectibles, and more. One of the ways to have a successful…
Altcoins
XENO starts VIP NFT trading service and collaborates with contemporary artist Hiro Yamagata
Hong Kong, Hong Kong, 24th December, 2020, // ChainWire //
The XENO NFT Hub (https://xno.live) will provide a crypto-powered digital items and collectables trading platform allowing users to create, buy, and sell NFTs. Additionally it will support auction based listings, governance and voting mechanisms, trade history tracking, user rating and other advanced features.
As a first step towards its fully comprehensive service, XENO NFT Hub launched a recent VIP service to select users and early adopters in December 2020 with plans for a full Public Beta to open in June 2021.
“NFTs are extremely flexible in their usage, from digital event tickets to artwork, and while NFTs have a very wide spectrum of uses and categories XENO will initially focus its partnership efforts and its own item curation on three primary areas: gaming, sports & entertainment, and collectibles.”, said XENO NFT Hub president Anthony Di Franco.
He also added “This does not mean we will prohibit other types of NFTs from our ecosystem However, it simply means that XENO’s efforts as a company will be targeted into these verticals initially as a cohesive business approach.”
Development and Procurement Lead, Gabby Dizon explained, “Despite our initial focus, we found ourselves with a unique opportunity to host some of the works of Mr. Hiro Yamagata. We are collaborating with Japanese artist Hiro Yamagata to enshrine some of his artwork into NFTs.”
Mr. Yamagata has…
-

 Blogs7 years ago
Blogs7 years agoBitcoin Cash (BCH) and Ripple (XRP) Headed to Expansion with Revolut
-

 Blogs7 years ago
Blogs7 years agoAnother Bank Joins Ripple! The first ever bank in Oman to be a part of RippleNet
-

 Blogs7 years ago
Blogs7 years agoStandard Chartered Plans on Extending the Use of Ripple (XRP) Network
-

 Blogs7 years ago
Blogs7 years agoElectroneum (ETN) New Mining App Set For Mass Adoption
-

 Don't Miss7 years ago
Don't Miss7 years agoRipple’s five new partnerships are mouthwatering
-

 Blogs7 years ago
Blogs7 years agoCryptocurrency is paving new avenues for content creators to explore
-

 Blogs7 years ago
Blogs7 years agoEthereum Classic (ETC) Is Aiming To Align With Ethereum (ETH)
-

 Blogs7 years ago
Blogs7 years agoIs Litecoin (LTC) Changing Its Game Plan By Going For Mass Adoption?